Cussins Enterprises LLC
Technology is a paint brush on the canvas of life.
What can we paint for you?

Cybersecurity News
Awareness of what is happening is the 1st to a secure system.Threat Post
| WP HTTP Error: cURL error 52: Empty reply from server |
Beeping Computer
| https://www.bleepingcomputer.com/feed/ is invalid XML, likely due to invalid characters. XML error: XML_ERR_NAME_REQUIRED at line 1, column 1342 |
Motherboard
| WP HTTP Error: A valid URL was not provided. |
Data Breeches
France Sees More Violent Attacks on Crypto Holders Than Any Other CountryOn May 24, 2026Source: DataBreaches.NetBy DissentCategories: Commentaries and Analyses, crypto Julian Lim reports: The hardest part of crypto security used to be keeping private keys away from ha… Read more |
UK: £355,880.10 confiscation order secured following proceeds of crime hearingOn May 23, 2026Source: DataBreaches.NetBy DissentCategories: Miscellaneous, Non-U.S. There’s a follow-up to the case of a motor insurance worker who received a suspended prison s… Read more |
Rhode Island’s workers’ compensation notifies those affected by January data breachOn May 23, 2026Source: DataBreaches.NetBy DissentCategories: Business Sector, Government Sector, Subcontractor, U.S. Rhode Island residents may understandably wonder about the state’s vendor security monitoring.… Read more |
UK: Victims feel ‘violated’ after water firm’s data breachOn May 23, 2026Source: DataBreaches.NetBy DissentCategories: Business Sector, Hack, ID Theft, Non-U.S. Oprah Flash reports: “Violated” and being “unable to trust” have been the fe… Read more |
Radiology Associates of Richmond discloses second data breach; 266k people affectedOn May 22, 2026Source: DataBreaches.NetBy DissentCategories: Breach Incidents, Health Data, HIPAA, U.S. On July 1, 2025, Radiology Associates of Richmond (“RAR”) reported a breach to HHS that… Read more |
Trump Mobile confirms it exposed customers’ personal data, unclear whether it will notify those affectedOn May 22, 2026Source: DataBreaches.NetBy DissentCategories: Business Sector, Hack, Subcontractor, U.S. Lorenzo Franceschi-Bicchierai reports: Phone provider Trump Mobile has confirmed that it was exposin… Read more |
Proposed State Laws For Breach Notification Could Reshape Incident Response PlansOn May 22, 2026Source: DataBreaches.NetBy DissentCategories: Breach Laws, Legislation, State/Local, U.S. Joseph Lazzarotti of JacksonLewis writes: State breach-notification laws continue to evolve, and leg… Read more |
How a consultant and a concert pianist from the Netherlands were arrested on suspicion of aiding NoName057(16)On May 22, 2026Source: DataBreaches.NetBy DissentCategories: Miscellaneous, Non-U.S. Officials allege that WorkTitans and MIRhosting were used to facilitate pro-Russian hackers and evad… Read more |
Hackers steal patient and billing data from German hospitals via third-party providerOn May 22, 2026Source: DataBreaches.NetBy DissentCategories: Health Data, Non-U.S., Subcontractor Daryna Antoniuk reports: German university hospitals are grappling with a large-scale patient data b… Read more |
Verus Hacker Returns $8.5M After Bridge Exploit DealOn May 22, 2026Source: DataBreaches.NetBy DissentCategories: Hack, crypto Do those who say never to pay ransomware or hack-and-leak criminals because it encourages more crime… Read more |
Cyberscoop
FBI warns about fast-growing phishing kit targeting Microsoft 365 usersOn May 22, 2026Source: CyberScoopBy Matt KapkoCategories: Cybercrime, Cybersecurity, Government, Research, Threats, access tokens, Arctic Wolf, cybercrime, device-code phishing, Federal Bureau of Investigation (FBI), Kali365, Microsoft, Microsoft 365, OAuth, phishing, phishing kit, Proofpoint Kali365, which was first observed in April, abuses legitimate Microsoft device authorization pages t… Read more |
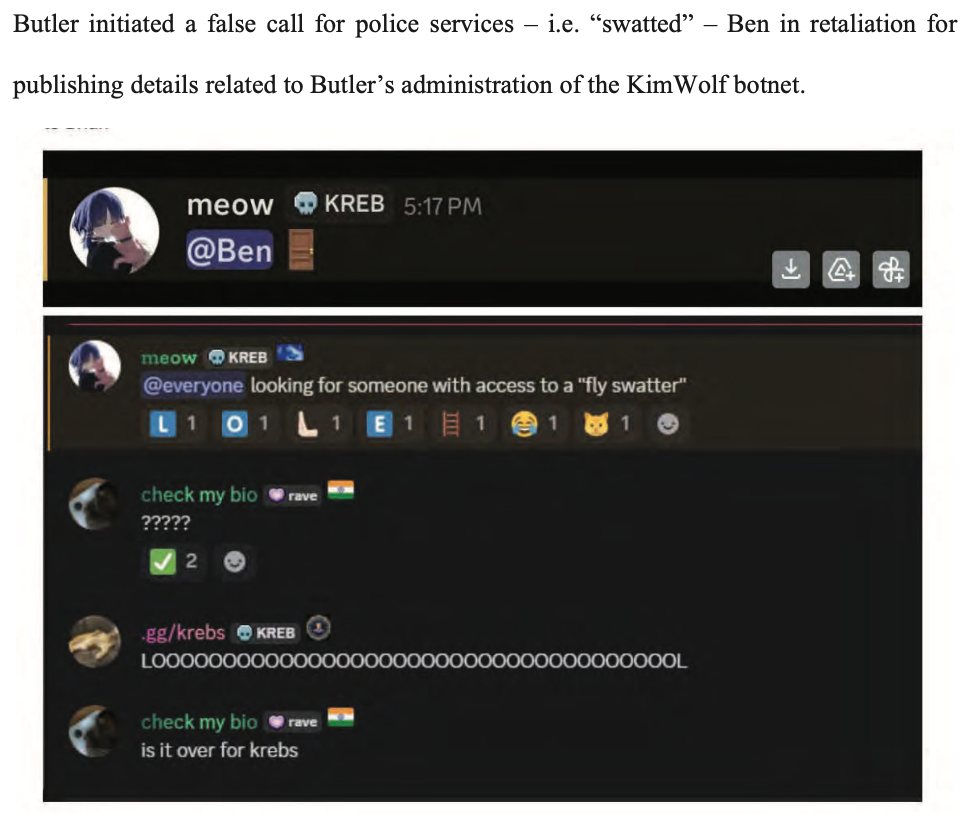
Alleged leader of Kimwolf, a sweeping botnet for cybercriminals, arrested in CanadaOn May 21, 2026Source: CyberScoopBy Matt KapkoCategories: Cybercrime, Cybersecurity, Aisuru, Arrest, botnet, Canada, cybercrime, DDoS, DDoS-for-hire, Department of Justice (DOJ), extradition, JackSkid, Kimwolf, Mossad Jacob Butler, a 23-year-old from Ottawa, awaits extradition to the United States and faces up to 10… Read more |
Lawmakers from both parties say CISA cuts have gone too farOn May 21, 2026Source: CyberScoopBy Greg OttoCategories: Government, budget, Congress, critical infrastructure, Cybersecurity and Infrastructure Security Agency (CISA), House Armed Services Committee, House Homeland Security Committee, Salt Typhoon Reps. Don Bacon, R-Neb., and James Walkinshaw, D-Va., found rare bipartisan agreement that the agenc… Read more |
Trump postpones executive order focused on AI securityOn May 21, 2026Source: CyberScoopBy djohnsonCategories: AI, Cybersecurity, Government, Policy, Technology, AI executive order, AI safety, AI security, Executive order, nsa, Treasury Department, Trump administration Under a draft executive order, the NSA, Treasury Department and other federal agencies would get 90-… Read more |
CISA chief frets about open-source vulnerabilities, delayed security improvementsOn May 21, 2026Source: CyberScoopBy Tim StarksCategories: Government, Technology, Cybersecurity and Infrastructure Security Agency (CISA), Nick Andersen, open source, TeamPCP Acting director Nick Andersen’s comments came as a wave of malware attacks hit tech that’s publicly… Read more |
European authorities take down prolific cybercrime VPN serviceOn May 21, 2026Source: CyberScoopBy Matt KapkoCategories: Cybercrime, Cybersecurity, Ransomware, cybercrime, Eurojust, Europe, Europol, France, The Netherlands, virtual private network (VPN) Officials arrested the alleged administrator of First VPN, seized its servers and domains. Europol s… Read more |
The readiness paradox: Why a false sense of cyber confidence is becoming a liabilityOn May 21, 2026Source: CyberScoopBy Greg OttoCategories: AI, Commentary, Artificial Intelligence (AI), op-ed, resilience As AI expands the attack surface and alert fatigue grows, cyber exposure management offers a clearer… Read more |
Meet Rampart and Clarity, Microsoft’s new red team combo AI agentsOn May 20, 2026Source: CyberScoopBy djohnsonCategories: AI, Cybersecurity, AI agents, Artificial Intelligence (AI), incident response, large language models, Microsoft, open source, prompt injection, red team, vulnerability reporting Microsoft’s AI red team lead talked to CyberScoop about the goals behind open sourcing a pair of sec… Read more |
GitHub says internal repositories were impacted in poisoned VS Code extension attackOn May 20, 2026Source: CyberScoopBy Greg OttoCategories: Threats, Aikido Security, Docker, GitHub, incident response, Microsoft, npm, open-source software, supply chain attacks, Visual Studio GitHub said late Tuesday that internal repositories were exfiltrated after an employee device was co… Read more |
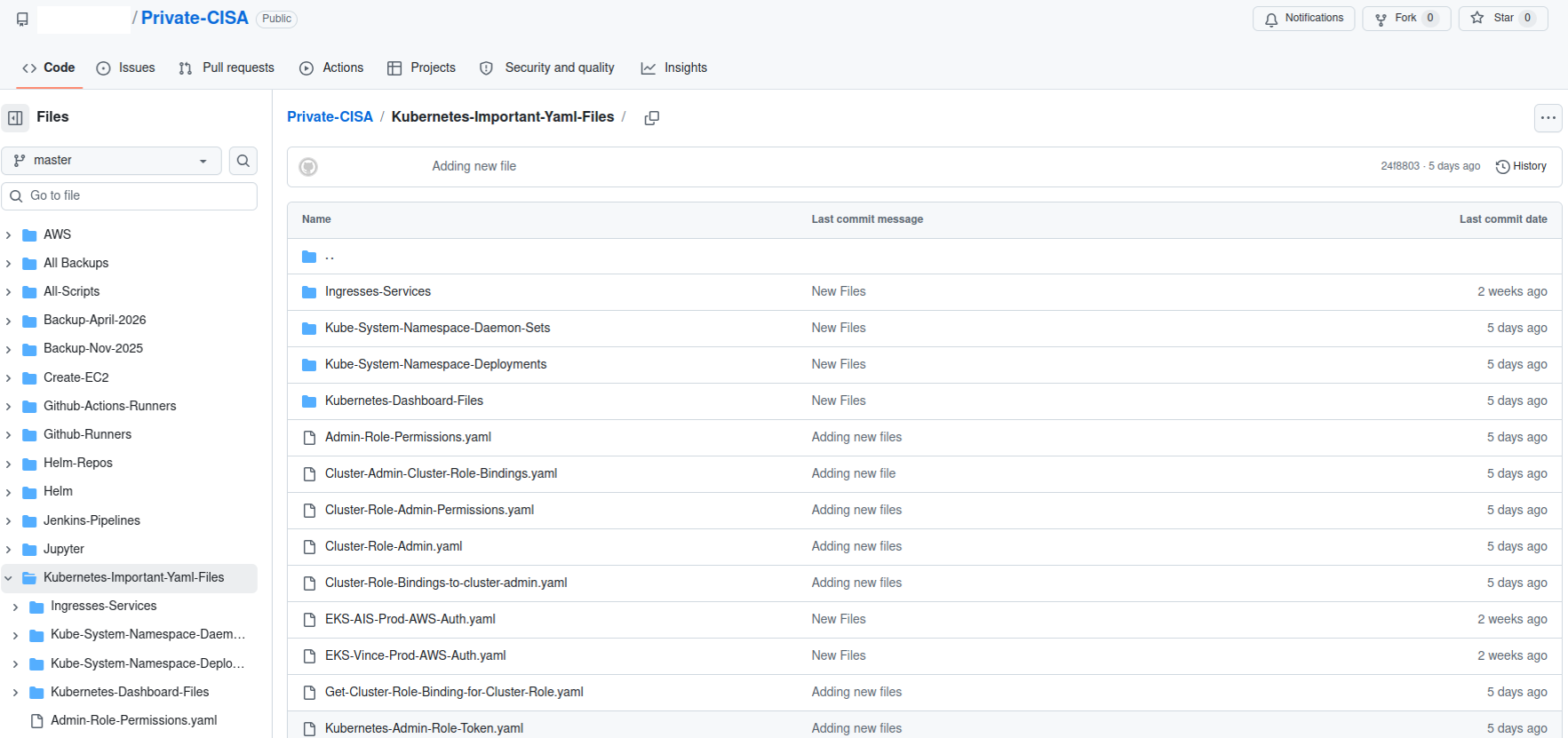
CISA credential leak raises alarms, and Capitol Hill demands answersOn May 19, 2026Source: CyberScoopBy Tim StarksCategories: Government, Technology, AWS, Bennie Thompson, Congress, Cybersecurity and Infrastructure Security Agency (CISA), Delia Ramirez, Department of Homeland Security (DHS), GitGuardian, GitHub, House Homeland Security Committee, Infoblox, maggie hassan, Nick Andersen, Nightwing, Rubrik, watchTowr A researcher who found a repository that leaked on GitHub said it was one of the worst he’s witnesse… Read more |
Krebs On Security
The Hacker News
 Lazarus Deploys RemotePE Memory-Only RAT Against Financial and Crypto FirmsOn May 25, 2026Source: The Hacker NewsByCybersecurity researchers have shed light on a cross-platform malware called RemotePE that has been… Read more Cybersecurity researchers have shed light on a cross-platform malware called RemotePE that has been put to use by the North Korea-linked Lazarus Group in attacks targeting financial and cryptocurrency organizations.
RemotePE, per NCC Group subsidiary Fox-IT, is part of a multi-stage attack chain that involves two loaders tracked as DPAPILoader and RemotePELoader.
"DPAPILoader decrypts and |
 TrapDoor Supply Chain Attack Spreads Credential-Stealing Malware via npm, PyPI, and CratesIOOn May 25, 2026Source: The Hacker NewsByA new coordinated cross-ecosystem software supply chain attack campaign has targeted npm, PyPI, and… Read more A new coordinated cross-ecosystem software supply chain attack campaign has targeted npm, PyPI, and Crates.io to distribute credential-stealing malware.
The campaign, codenamed TrapDoor, spans more than 34 malicious packages across over 384 versions. The earliest activity was recorded on May 22, 2026, at 8:20 p.m. UTC, with new packages published to the ecosystems in waves from a cluster of |
 npm Adds 2FA-Gated Publishing and Package Install Controls Against Supply Chain AttacksOn May 23, 2026Source: The Hacker NewsByGitHub has rolled out new controls for npm to improve the security of the software supply chain, giv… Read more GitHub has rolled out new controls for npm to improve the security of the software supply chain, giving maintainers the ability to explicitly approve a release prior to the packages becoming publicly available for installation.
Called staged publishing, the feature is now generally available on npm. It mandates that a human maintainer pass a two-factor authentication (2FA) challenge to approve |
 Packagist Supply Chain Attack Infects 8 Packages Using GitHub-Hosted Linux MalwareOn May 23, 2026Source: The Hacker NewsByA new "coordinated" supply chain attack campaign has impacted eight packages on Packagist including… Read more A new "coordinated" supply chain attack campaign has impacted eight packages on Packagist including malicious code designed to run a Linux binary retrieved from a GitHub Releases URL.
"Although the affected packages were all Composer packages, the malicious code was not added to composer.json," Socket said. "Instead, it was inserted into package.json, targeting projects that ship JavaScript |
 Claude Mythos AI Finds 10,000 High-Severity Flaws in Widely Used SoftwareOn May 23, 2026Source: The Hacker NewsByAnthropic on Friday disclosed that Project Glasswing has helped uncover more than 10,000 high- or cr… Read more Anthropic on Friday disclosed that Project Glasswing has helped uncover more than 10,000 high- or critical-severity vulnerabilities across some of the most "systemically" important software across the world since the cybersecurity initiative went live last month.
Project Glasswing is a defensive effort launched by the artificial intelligence (AI) company to secure critical global software |
 Laravel-Lang PHP Packages Compromised to Deliver Cross-Platform Credential StealerOn May 23, 2026Source: The Hacker NewsByCybersecurity researchers have flagged a fresh software supply chain attack campaign that has target… Read more Cybersecurity researchers have flagged a fresh software supply chain attack campaign that has targeted multiple PHP packages belonging to Laravel-Lang to deliver a comprehensive credential-stealing framework.
The affected packages include -
laravel-lang/lang
laravel-lang/http-statuses
laravel-lang/attributes
laravel-lang/actions
"The timing and pattern of the newly published tags |
 LiteSpeed cPanel Plugin CVE-2026-48172 Exploited to Run Scripts as RootOn May 23, 2026Source: The Hacker NewsByA maximum-severity security vulnerability impacting LiteSpeed User-End cPanel Plugin has come under… Read more A maximum-severity security vulnerability impacting LiteSpeed User-End cPanel Plugin has come under active exploitation in the wild.
The flaw, tracked as CVE-2026-48172 (CVSS score: 10.0), relates to an instance of incorrect privilege assignment that an attacker could abuse to run arbitrary scripts with elevated permissions.
"Any cPanel user (including an attacker or a compromised account) may |
 Drupal Core SQL Injection Bug Actively Exploited, Added to CISA KEVOn May 23, 2026Source: The Hacker NewsByThe U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a recently patched critic… Read more The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a recently patched critical security flaw impacting Drupal Core to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation.
The vulnerability in question is CVE-2026-9082 (CVSS score: 6.5), an SQL injection vulnerability affecting all supported versions of Drupal Core.
"Drupal Core |
 First VPN Dismantled in Global Takedown Over Use by 25 Ransomware GroupsOn May 22, 2026Source: The Hacker NewsByAuthorities in Europe and North America have announced the dismantling of a criminal virtual private… Read more Authorities in Europe and North America have announced the dismantling of a criminal virtual private network (VPN) service used by criminal actors to obscure the origins of ransomware attacks, data theft, scanning, and denial-of-service attacks.
Codenamed Operation Saffron, the disruption of First VPN Service was led by France and the Netherlands, with several other nations supporting the |
 Ghostwriter Targets Ukraine Government Entities with Prometheus Phishing MalwareOn May 22, 2026Source: The Hacker NewsByThe Belarus-aligned threat actor known as Ghostwriter (aka UAC-0057 and UNC1151) has been observed u… Read more The Belarus-aligned threat actor known as Ghostwriter (aka UAC-0057 and UNC1151) has been observed using lures related to Prometheus, a Ukrainian online learning platform, to target government organizations in the country.
The activity, per the Computer Emergency Response Team of Ukraine (CERT-UA), involves sending phishing emails to government entities using compromised accounts. It's been |
How Can We Help?